Information Security Awareness Training & Ongoing Awareness
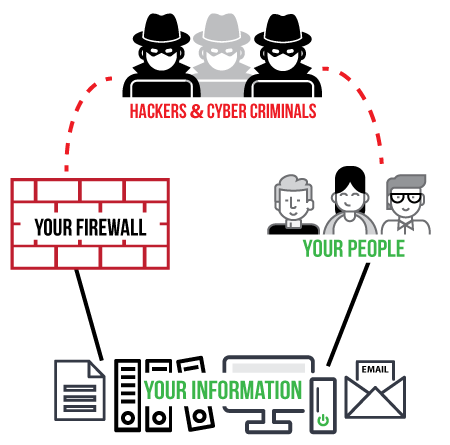
The right awareness for every User requires not only annual certifications but ongoing awareness (daily, weekly, monthly, situational, etc.) to eliminate commonly exploited GAPS allowing ransomware, malware, and other evilware to gain unauthorized access to your valuable, sensitive, and proprietary data. In other words, the right awareness is important to keep your people, organization, and information safe.
We do the research and prepare the information for your Users so you don’t have to!
Awareity delivers:
• The most complete software-as-a-service (SaaS) (tools, reports, compliance documentation, audit documentation, etc.).
• The most effective Information Security Awareness Training, Cyber Security Training, and Hacker Awareness training for eliminating dangerous and costly GAPS that grow bigger and bigger starting the day after conventional annual training is completed.
• Efficient and completely customizable policy management solutions to match an organization’s specific and custom needs with automated management and reminders for Users and Administration as well as legal-ready documentation and audit-ready reporting.
• Additional specialized awareness training for HIPAA, FERPA, and PCI including awareness reminders and updates throughout the year.
What our clients are saying:
“An easy to manage and effective online tool which has greatly reduced the time we spend delivering, tracking, and responding to user training and compliance. Additionally, we are very pleased with the timely and expert support we received from the Awareity staff.”
“We have been utilizing Awareity’s Platform for over five years and every year we find more and more ways to utilize it to save money and improve our employees’ awareness.”
“Training adds value as it makes County employees aware of ongoing dangers/pitfalls and provides helpful suggestions as to how the average user can enhance security by putting these suggestions into practice.”